Train to think and act like a hacker — but for good. This program covers the entire ethical hacking lifecycle: reconnaissance, scanning, gaining access, maintaining access, and covering tracks. You’ll master 550+ attack tools and techniques in a legal, controlled environment, preparing you for the EC‑Council C|EH v13 certification exam.
✔ 70% hands-on labs • 150+ real‑world attack scenarios • Official EC‑Council courseware • Capstone project (end‑to‑end penetration test) • 24/7 cyber range access.
Footprinting, scanning, enumeration, vulnerability assessment, system hacking, malware threats, sniffing, social engineering, DoS/DDoS, session hijacking, web app hacking, SQL injection, cloud computing hacking, cryptography, and penetration testing reporting.
Basic understanding of networking (TCP/IP) and operating systems (Windows/Linux). No prior hacking experience required — we start from fundamentals.
Conduct a full network penetration test, exploit web application vulnerabilities (OWASP Top 10), perform wireless cracking, create a ransomware simulation, and write professional pentest reports.
Exam vouchers (optional), mock tests, resume review, portfolio development, and interview preparation for Penetration Tester, SOC Analyst, Security Consultant, and Red Team Engineer roles.
Tailored ethical hacking upskilling for security teams and enterprises
Choose from CEH, PenTest+, or red teaming tracks aligned to your security maturity.
Hands-on practice in isolated, real‑world network environments with legal safe harbor.
Monitor progress and skill gaps with detailed analytics and attack simulation scoring.
Volume discounts for teams of 10+, plus pay-as-you-go options.
Dedicated cybersecurity mentors to assist your learners anytime.
Single point of contact for seamless training delivery.

Get a custom quote for your organization’s ethical hacking training.
From Passive Reconnaissance to Advanced Persistence
Use OSINT tools, DNS interrogation, WHOIS, search engines, and social media to gather target intelligence.
Master Nmap, masscan, and advanced scanning techniques. Enumerate services, users, and shares via NetBIOS, SNMP, LDAP, and SMB.
Use Nessus, OpenVAS, and manual testing to identify flaws. Exploit with Metasploit, custom scripts, and public exploits.
Crack passwords (John, Hashcat), escalate privileges, maintain persistence, and cover tracks using rootkits and steganography.
Perform SQL injection, XSS, CSRF, command injection, file inclusion, and IDOR using Burp Suite and ZAP.
Attack cloud misconfigurations (AWS, Azure, GCP), hack wireless networks (WEP/WPA/WPA2), and exploit IoT device vulnerabilities.
Ideal Candidates for Certified Ethical Hacker (C|EH) v13 Certification
Designed for IT professionals and beginners who have basic networking and operating system knowledge. This program builds your ethical hacking skills from ground zero to advanced real‑world exploitation and reporting, giving you the confidence to pass the EC‑Council C|EH v13 exam and excel in penetration testing roles. Average salaries for Certified Ethical Hackers in India range from ₹5 Lakhs to ₹15+ Lakhs per year.
Your Step‑by‑Step Path to Ethical Hacking Certification
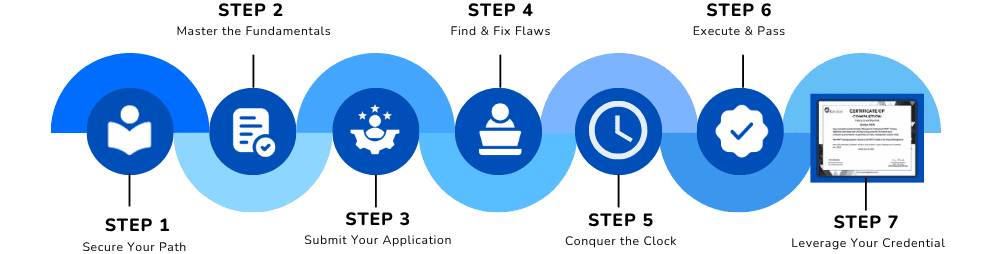
Master ethical hacking concepts, footprinting, and passive information gathering techniques.
What You Need Before You Start
Objective: To certify your ability to identify, exploit, and report vulnerabilities in target systems using ethical hacking methodologies. Candidates should have:
Understanding of TCP/IP, OSI model, subnets, DNS, HTTP/S, and common ports. (CompTIA Network+ level recommended).
Comfortable with command line (cmd, PowerShell, bash), file system, and user administration.
No prior hacking experience required — we start with ethical and legal foundations, then progress to advanced exploits.
Comprehensive CEH v13 modules covering all 20 attack domains
Hacking phases, types of attacks, legal framework, and code of ethics.
Gather information using Google hacking, Shodan, theHarvester, Maltego, and social media reconnaissance.
Port scanning, OS detection, version detection with Nmap, masscan, and Zenmap.
Enumerate NetBIOS, SNMP, LDAP, SMB, and NFS to extract users, shares, and services.
Use Nessus, OpenVAS, and manual techniques to discover weaknesses.
Password attacks (John, Hashcat, Responder), privilege escalation (Windows/Linux), and maintaining access (backdoors, rootkits).
Create and detect malware, use packers/crypters, and analyze with static/dynamic tools.
Perform ARP spoofing, MAC flooding, and DNS poisoning. Use Wireshark, Ettercap, and BetterCAP.
Phishing, vishing, tailgating, and impersonation; use SET (Social-Engineer Toolkit).
Launch SYN flood, UDP flood, and application-layer attacks. Hijack sessions via prediction or XSS.
SQL injection, NoSQL injection, command injection, and authentication bypass techniques.
Exploit cross‑site scripting, request forgery, server‑side request forgery, and insecure direct object references.
Crack WEP, WPA/WPA2 handshakes with Aircrack‑ng, Reaver, and PMKID attacks.
Identify vulnerable IoT devices, attack Zigbee, BLE, and MQTT protocols.
Exploit overly permissive IAM, public storage buckets, and insecure APIs on AWS/Azure/GCP.
Container breakout, privilege escalation, and insecure Kubernetes RBAC.
Identify weak ciphers, perform hash collisions, and implement PKI misuse.
Use fragmentation, encoding, and tunneling to bypass security controls.
Execute a complete pentest: reconnaissance → exploitation → post‑exploitation → reporting.
Write executive and technical reports, present findings, and practice with CEH v13 mock exams.
Lifetime Access
Real Pentest Projects Included
Mentor Support
Practice Assignments
Certificate Preparation
Join 27,000+ successful ethical hackers who launched their cybersecurity careers with our hands‑on CEH training. C|EH is the #1 ethical hacking certification and is trusted by governments, militaries, and Fortune 500 companies worldwide.
✅ Limited seats available for the upcoming batch • EMI options available • Official EC‑Council curriculum