The CISSP is the most globally recognized certification in the information security field. This comprehensive program prepares you for the (ISC)² CISSP exam by covering the eight domains of the (ISC)² CBK. You will learn from experienced CISSP instructors, work through real‑world scenarios, and master the skills required to lead security programs and teams.
✔ 50% scenario‑based learning • 100+ practice questions • Official (ISC)² student guide • Capstone: enterprise security program design • 24/7 mentor support.
Security governance, risk management, compliance, asset security, security architecture, network security, identity management, security assessment, security operations, software development security, BCP/DRP, incident response, cryptography, legal & regulatory compliance.
Minimum 5 years of cumulative, paid work experience in two or more of the eight CISSP domains. One year waiver available with a 4‑year degree or approved credential.
Conduct a full risk assessment for a global enterprise, design a security architecture for a financial institution, create an incident response playbook, and develop a business continuity plan.
Exam vouchers, mock exams, resume review, endorsement assistance, and interview preparation for CISO, Security Manager, Security Architect, and Senior Security Engineer roles.
Tailored CISSP upskilling for security teams and enterprises
5‑day intensive, weekend, or evening tracks to fit team schedules.
Access to 50+ scenarios covering security program management, breach response, and compliance design.
Monitor progress and skill gaps with detailed analytics and mock exam performance.
Volume discounts for teams of 10+, plus pay-as-you-go options.
Dedicated CISSP‑certified mentors to assist your learners anytime.
Single point of contact for seamless training delivery.

Get a custom quote for your organization's CISSP training.
Master All 8 Domains of (ISC)² CISSP CBK
Confidentiality, integrity, availability; governance; compliance; legal & regulatory issues; risk analysis; business continuity; security awareness.
Data classification, ownership, privacy, retention, handling requirements, and secure data disposal.
Secure design principles, enterprise architecture, virtualization, cryptography, and physical security.
Network architecture, secure protocols, network components, and secure communication channels.
Authentication, authorization, identity lifecycle, federation, and access control mechanisms.
Vulnerability assessment, penetration testing, security audits, and log analysis.
Incident response, monitoring, investigations, disaster recovery, and physical security operations.
Secure SDLC, DevSecOps, security controls in development, and software vulnerabilities.
Ideal Candidates for CISSP Certification
Designed for experienced security practitioners with at least 5 years of relevant work experience. This program elevates your ability to design, implement, and manage best‑in‑class security programs, giving you the confidence to pass the (ISC)² CISSP exam and advance to leadership roles. Average salaries for CISSP holders in India range from ₹15 Lakhs to ₹40+ Lakhs per year, with global recognition as a senior‑level credential.
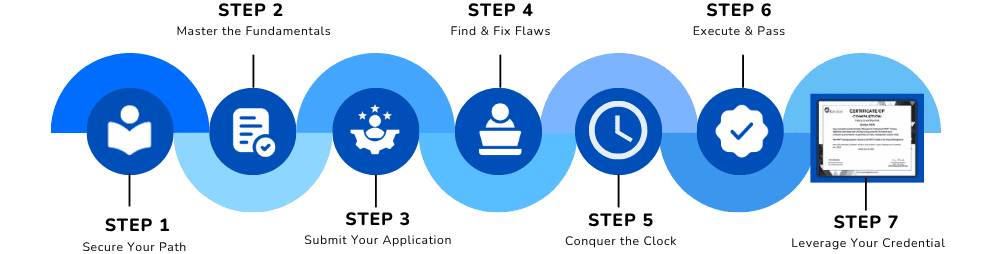
Your Step‑by‑Step Path to CISSP Success
Master governance, risk compliance, and business continuity – the backbone of the CISSP.
What You Need Before You Start
Objective: To certify advanced knowledge and leadership ability in information security. Candidates must meet the following requirements:
Experience must be in two or more of the eight CISSP domains. A 4‑year university degree or (ISC)² approved credential can substitute for one year of experience.
After passing the exam, you must be endorsed by an (ISC)² certified professional in good standing who can attest to your professional experience.
All CISSP holders must agree to adhere to the (ISC)² Code of Ethics and maintain continuing professional education (CPE) credits annually.
Comprehensive coverage of all 8 CISSP domains as per (ISC)² CBK
Security governance principles, legal & regulatory compliance, professional ethics, and security policies.
Risk assessment frameworks, risk response, business continuity planning, and disaster recovery.
Design effective security awareness programs and measure their effectiveness.
Define asset classification, roles (data owner, custodian, user), and handling requirements.
Privacy principles (GDPR, CCPA), data retention policies, and secure disposal.
Defense in depth, least privilege, zero trust, and enterprise security architecture frameworks (SABSA, TOGAF).
Symmetric/ asymmetric encryption, hashing, digital signatures, PKI, and cryptographic attacks.
Site design, access controls, environmental controls, and physical security threats.
OSI/TCP‑IP models, secure protocols (SSL/TLS, IPsec, SSH), network segmentation, and wireless security.
Firewalls, IDS/IPS, VPNs, SD‑WAN, and secure remote access methods.
Factors of authentication, MFA, SSO, federation (SAML, OAuth), and directory services (LDAP, Active Directory).
Provisioning, deprovisioning, privileged access management (PAM), and access review.
Types of tests (black/white/grey box), methodologies, tools (Nessus, Metasploit), and reporting.
Internal vs external audits, log management, SIEM, and continuous monitoring.
IR framework, detection, containment, eradication, recovery, and post‑incident activity.
BCP/DR plan execution, backup strategies, failover testing, and recovery objectives (RTO/RPO).
Personnel security, visitor control, environmental monitoring, and incident coordination.
Security integration in requirements, design, coding, testing, deployment, and maintenance.
Code reviews, static/dynamic analysis, software composition analysis (SCA), and vulnerability management.
OWASP Top 10, memory corruption, injection flaws, and secure coding practices.
Understand Computerized Adaptive Testing (CAT), how to eliminate distractors, and manage time.
Full‑length mock exams with detailed explanations, weak‑area analysis, and targeted remediation.
Create a comprehensive security roadmap integrating all 8 domains for a real‑world enterprise case study.
Lifetime Access
Real Leadership Scenarios
Mentor Support (CISSP holders)
Practice Exams (1,500+ questions)
Certificate Preparation
Join 21,000+ successful CISSP holders who elevated their careers with our comprehensive training. The CISSP is consistently ranked as the highest‑paying IT certification worldwide.
✅ Limited seats available for the upcoming batch • EMI options available • Includes (ISC)² endorsed practice exams